In these times of isolation, the world plus dogs, cats and the occasional really cute squeaky thing eating sweet potato, has turned to the Internet to provide a communications mechanism for the people to work, play, rant, consume art (thank you all of the artists), and the seedy rest of it.
Of course during times of high consumption, the applications facilitating this communication are coming under increased scrutiny from security ‘researchers’ both well and less so well minded.
There have been quite a few shrieking headlines about two platforms in particular, one for fun; Houseparty, and one which is being used by both businesses for the daily stand-up meetings (argh), all-hands meetings (argh argh) and the dreaded town-hall sessions as well as actual productive sessions; Zoom. You may recall that the good minded people at Zoom were giving the tech away to schools.
We thought it might be a good idea to go over what is being claimed and what the implications are for these two products and perhaps try and turn down the heat into something sensible.
Let’s talk about Houseparty first. This week, it was claimed that Houseparty had been badly jacked and was being used to steal bank account details, emails, abduct small children, the whole bit. Now this is almost certainly (we never say never) absolute tripe and not true, so much so that the makers of Houseparty, Epic Games has put up a $1 Meeelion bounty for someone to identify the smearers.
Since the infamous Sony games hack of 2011 , it is a fact that Games vendors are amongst the most serious outfits regarding security. Security is built in from the ground up and rarely retrofitted.
Our view is that this is exactly what Epic are suggesting - time will tell. Houseparty is probably just fine to use. It certainly doesn’t have the Copyright bots that Facebook does which turns streams of DJs playing other people’s records (imagine?) off, ruining the party.
As a consequence of the Houseparty noise, many people deleted the app and turned to Zoom. In the last week, a couple of issues have surfaced with this platform. Unfortunately, these appear to be very accurate and a bit worrying. (Does this sound anything like a game of Battleships to anyone else?).
The first issue, which has been covered by other security researchers, such as his emminence, the one and only, we are not worthy (really), Brian Krebs, is pretty much down to a default behaviour/misconfiguration issue that many organisations are falling foul to with Zoom.
Back in the dawn of time, Zoom meetings did not require a password by default, this was added in late 2019, but many people are ‘opted out’ because of prior lazy settings, fat fingers, whatever. This means that many meetings are going ahead without passwords and are being listened into by hackers, script kiddies and the like for both general nuisance making and for more serious purposes.
Some bored researchers have even created a really old school looking piece of code called zWarDial which trawls through potential Zoom meetings and identifies open ones. The aged and derelict amongst us will remember ‘WarDialing’ being code that phoned up sequential phone numbers looking for modems, as used extensively by Kevin Mitnick in real life and by David Lightman (played by Matthew Broderick) in the film War Games. “Shall we play a game?”.
This is easily fixed by using best practice configuration as documented in Mr Krebs’ fantastic piece above.
Unfortunately, Zoom is also suffering from a more malicious nasty which is the ability to use the Windows client to execute arbitrary code on a machine remotely. There are workarounds to prevent this including setting a strong password and changing security policy settings. These are detailed in this piece from the hard working people at The Hacker News.
If you are a corporate Zoom user, have a read of both The Hacker News piece and Mr Krebs. Zoom has had a number of security issues in the past, so be cautious about what you use it for. One of our associates drew our attention to this interesting advice.
What would you use instead? You may well ask.
Three of the main alternatives for corporate use are Microsoft Teams, Cisco Webex (hard to type that without having to check in to therapy after years of mind numbing totally unproductive and massively frustrating Webex meetings, but heyho) and Slack.
These all have issues which you should be aware of, almost all of which are about correct configuration (Two Factor authentication etc.). There are differences in how the communications are encrypted at rest and in transit. Slack for instance does not have end-to-end encryption, Webex and Microsoft Teams both do.
Microsoft has four development categories for security compliance (who knew?), pithily named A, B, C and D. Teams is a category D product and is about as secure as anything you can get in this space. Other than the confusing data flows, Teams is pretty solid (so far) and you can rest easy (for now).
For private conversations mobile to mobile, many people use WhatsApp. We don’t really trust WhatsApp and prefer Wire for secure comms. The intro screen is groovy and it is very safe. If you need to discuss hacking Zoom with your 11 year old pal from Estonia, Wire should be your choice.
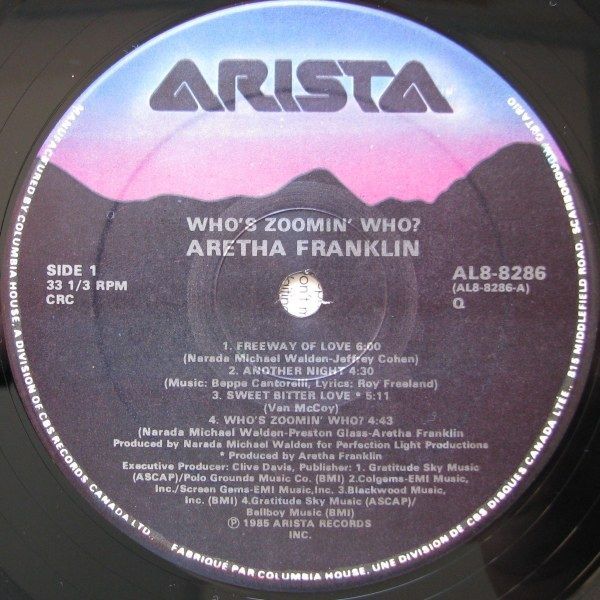
Apologies for the lack of music references this week, apart from the title. The Aretha Franklin tune even has the lyric ‘now the fish jumped off the hook’ in it so we are almost certainly missing a trick.
If you enjoy reading this please register to receive automatic updates, invites to crazy parties and access to occasional analysis and research.
Hope you and yours are keeping well and bearing up. Hide the knives.